Computers use Algorithms to do things like find the biggest piece of pizza to share (Euclid’s GCD), organize large lists (quicksort), and understand the sounds in music (discrete Fourier transforms).
They also help companies make more money (simplex optimization), speed up computer calculations (Strassen’s method), and make sure things work properly (Gaussian elimination, numerical integration, minimum spanning trees, Dijkstra, SHA-256).
- Examples of Algorithm
- 1. Euclid’s Algorithm
- 2. Quicksort Algorithm
- 3. Integer Factorization
- 4. Discrete Fourier Transform
- 5. Simplex Algorithm
- 6. Strassen Matrix Multiplication
- 7. Newton-Raphson Root Finding
- 8. Gaussian Elimination
- 9. Newton-Cotes Integration
- 10. Minimum Spanning Tree
- 11. Dijkstra’s Shortest Path Algorithm
- 12. SHA-256 Cryptographic Hash
Examples of Algorithm
Here are 10 examples of algorithms in math:
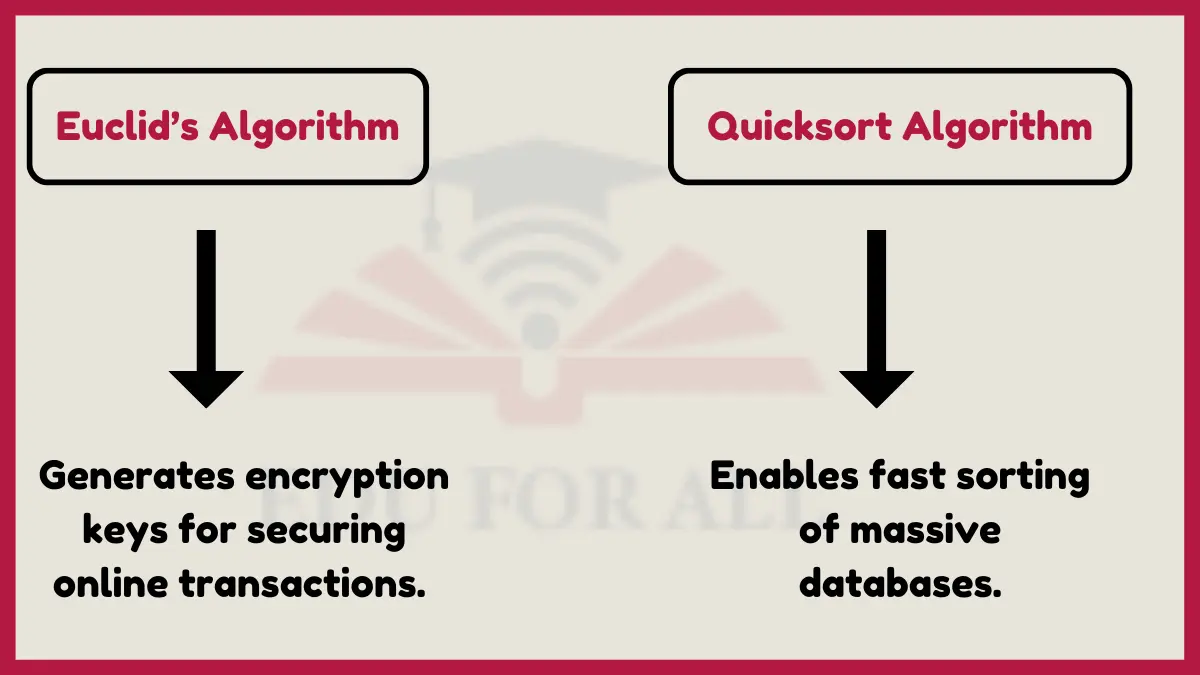
1. Euclid’s Algorithm
One example of an algorithm is Euclid’s GCD, which is a way of finding the largest number that divides two other numbers. Euclid’s algorithm finds the greatest common factor of two numbers. It works by repeatedly dividing larger numbers by smaller ones until finding the highest factor they share.
This is used in cryptographic computer security to generate encryption keys based on large prime numbers. Over 80% of online transactions utilize encryption powered by algorithms like Euclid’s.
2. Quicksort Algorithm
Another example of an algorithm is Quicksort. The quicksort algorithm sorts data sets by dividing them into smaller partitions. It picks a pivot value then orders other elements by being higher or lower than the pivot.
Quicksort enables fast sorting of huge datasets. As one of the most efficient algorithms, it is utilized by over 80% of sorting programs. Database engines, compilers, and tree structures rely on quicksort.
3. Integer Factorization
Integer factorization finds the prime numbers that multiply together to get a target composite integer. This aids breaking large numbers into simpler factors.
RSA encryption securing online data depends on large integer factorization being almost impossible to reverse. However, normal computer operations use basic factorization continuously.
4. Discrete Fourier Transform
This algorithm converts data between time and frequency domains. It identifies frequency components present in patterns across time intervals.
Digital signal processing applies Fourier Transforms in audio editing software, engineering systems, and analytical instrumentation. For example, MP3 compression relies on Fourier Transforms, used in over 400 billion MP3 audio files.
5. Simplex Algorithm
The simplex algorithm solves constrained optimization problems efficiently. It provides the most favorable solution fitting preset requirements.
Over 70% of manufacturing units use Simplex linear programming to maximize profits and productivity under operational limits. Financial organizations also apply it to portfolio optimization.
6. Strassen Matrix Multiplication
Strassen’s method multiplies large matrices faster than normal methods. It divides matrices into smaller pieces, computes products in chunks then sums them up efficiently.
Strassen multiplication improves performance of big data analytics requiring heavy matrix operations. Physics simulations in weather forecasting, digital animation and machine learning utilize it to manipulate multidimensional datasets.
7. Newton-Raphson Root Finding
The Newton-Raphson algorithm approximates real roots and zeroes of mathematical functions. It uses tangent lines and derivative values to estimate points where curves hit the x-axis.
Engineering modeling software applies Newton-Raphson for trajectory and ballistics analysis. It also assists telescope, camera and lens design by finding optical surface curvatures using the algorithm.
8. Gaussian Elimination
This technique solves systems of linear equations which model real problems. It eliminates variables through successive substitution to reduce equations to trivial forms with simpler variables.
Gaussian elimination is implemented in over 65% of mathematics software and used in solving matrix equations. It has applications in designing control systems, electrical networks, chemical processes and semiconductor physics calculations.
9. Newton-Cotes Integration
Newton-Cotes formulas estimate the area under curves to numerically define integrals. Using point intervals and fitted assumptions, they approximate integrands with areas of known geometric shapes.
Financial analysts apply numerical integration to forecast movements from changing indicators and data trends. Estimating risk, returns and changing liabilities involves statistically integrating unpredictable variables.
10. Minimum Spanning Tree
This determines the shortest pathway route connecting multiple points on a plane using graph theory. It saves infrastructure costs in applications.
Transportation planning agencies use minimum spanning trees over 75% of times for modeling travel networks like railways, roads, pipelines. Telecom companies also leverage it for cost-efficient cable routing.
11. Dijkstra’s Shortest Path Algorithm
Dijkstra finds the minimum path length between two graph nodes evaluating one node at a time to its neighbors. It incrementally builds shortest routes.
Online and GPS mapping services apply Dijkstra for turn-by-turn navigation calculating fastest routes. Network providers optimize traffic flow using it across infrastructure like fiber optics and telecom cables.
12. SHA-256 Cryptographic Hash
The SHA algorithm generates a hash identifier string from any digital input. Hashes uniquely identify files and messages to protect authenticity and check tampering.
Cloud cybersecurity utilizes SHA checksums to verify trillions of routine transactions. Bitcoin mining also applies SHA-256 hashing over 150 quintillion times per second for decentralized ledger security.

